According to public information (1) provided by the US Department of Health and Human Services (2) regarding the number of health data records that were subject of undue exposure through security breach, this year and as of July 7 2015, these amounted to 94.074.319. Compared to the total amount of health data records that were exposed throughout the last year (3), the growth of this indicator is around 752%!!!
It is necessary to note that this information only includes security breaches occurred in the US and registered under the HIPAA regulations(4), and that those breaks are only concerning those who have unduly exposed health information for 500 individuals or more, getting out the lower exposure range. But why is this “new appetite” for health data over other valuable data, such as financial? What for is this data used? What is in the origin of these security breaches high numbers? How much does a health data record worth?
Health data is usually rich in patients information, making up this closely related to that of their health character (diseases, medical prescriptions, diagnostics results, and more…) but also containing data related to payment means, health plans associated, family home and employment addresses, date of birth and more other information from personal and private nature. It is estimated that health data is worth, right now in the internet black market, between 50 to 60 USD per record (5)! It is thus easy to understand why are these so desirable by Hackers.
Whether for sale of these data to other criminals such as identity theft purposes for further illegal activities, either to directly or indirectly carry out acts of blackmail and extortion to attacked organizations, or for illegal resale of these data to other legally established organizations using these for illicit purposes (profiling for sale to lending evaluators or health insurance, for instance), the fact is that health data worth trillions of euros indeed!
Cumulatively, healthcare organizations and hospitals, use more and more US services provider information process their clients data (6). While technology systems to organizations with financial data, under huge media exposure and negative impacts in their image regarding the results of effective security breaches we have seen regularly, especially in the last decade, they strengthened their systems and information security programs, the organizations directly related to health data have not done the same.
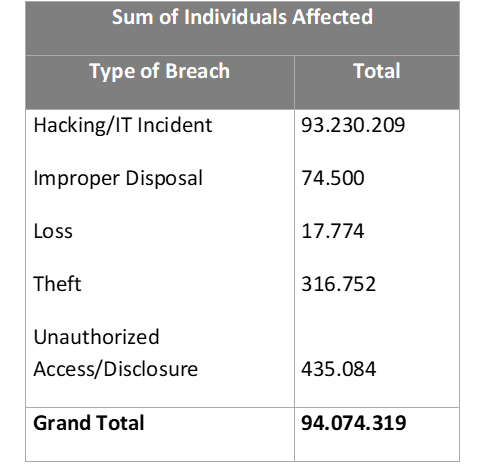
From the table below, constructed based on available data (1), we can easily verify that the type of security breaches that gave rise to the undue exposure is directly related to technologies field (7).
Sum of Individuals Affected
| Type of Breach | Total |
|---|---|
| Hacking/IT Incident | 93.230.209 |
| Improper Disposal Loss | 74.500 |
| Theft | 17.774 |
| Unauthorized | 316.752 |
| Access/Disclosure | 435.084 |
| Grand Total | 94.074.319 |
It is therefor critical that any organization that deals with health data promotes the improvement of their information systems security, and beyond. Surely soon, those that not ensure a well conceived Information Security Management System, will suffer some kind of attack, which might be extremely serious and may endanger the organization survival itself.
Adopting good information security practices associated to one security management model in accordance with the requirements of NP ISO/IEC 27001:2013 and others, certainly when an attack occurs (and it will take place!) the organization will be previously prepared for it, triggering an appropriate response to the incident in question and, most likely by reducing or cancelling the negative impact on the business.
Several organizations in Portugal and around the world have already adopted this standard of excellence for effective information security management, either to protect their own information or that which is under their responsibility, continuously increasing their resilience to adverse incidents.
Referrals:
- https://ocrportal.hhs.gov/ocr/breach/breach_report.jsf
- U.S. Department of Health & Human Services (www.hhs.gov)
- 12.503.190 records
- HIPAA Privacy Rule, which protects the privacy of individually identifiable health information; the HIPAA Security Rule, which sets national standards for the security of electronic protected health information; the HIPAA Breach Notification Rule, which requires covered entities and business associates to provide notification following a breach of unsecured protected health information; and the confidentiality provisions of the Patient Safety Rule, which protect identifiable information being used to analyze patient safety events and improve patient safety.
Brian Honan, BH Consulting, “Data Protection / Security Issues & Interoperability / Cybercrime Marketplace”, Maastritcht, 24th June 2015 - More than 528,000 health care providers and hospitals had registered in federal incentive programs for electronic health records as of February 2015, according to the U.S. Centers for Medicare and Medicaid services.
- To point out that, because the number of security breaches due to “hacking” or IT incident is 1 to 10 compared to other types of breaches, the fact is that every time this threat appears in an information system, the number of displayed records is usually very high.